Message from the top of Red Hat Summit
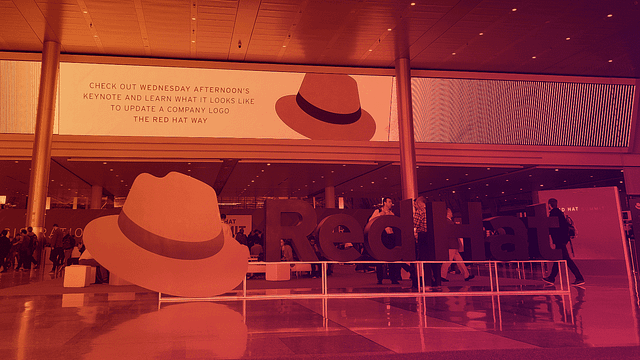
Year after year, there seem to be more conferences, conventions, meetups, and user groups – just like acronyms, a never-ending supply in the Technology space! Here at Fierce Software we proudly support our vendors, and we’re known for making a show of it too. We don’t just wave our flags at events, we make our[…]





